SimpLocker
Summary
Details
Simplelocker is a ransomware discovered in 2014. It encrypts user’s multimedia files stored in the SD card. The original files are deleted and the malware asks a ransom to decrypt the files. Our sample displays instructions in Russian. Simplelocker communicates with a server hidden behind a Tor network to receive orders, for example the payment confirmation.
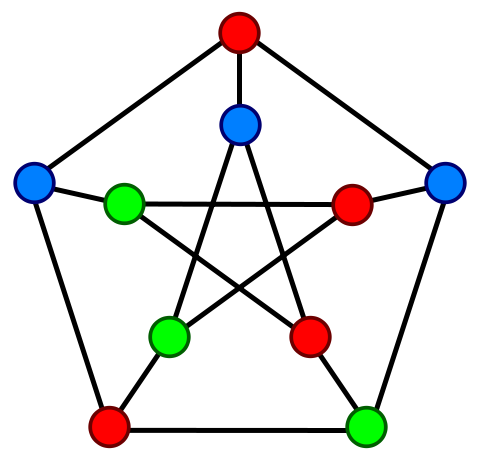
Simplelocker relies on the execution of three main independent processes. First, rg.simplelocker runs the graphical interface, the main service and the different repetitive tasks. Second, libprivoxy.so and tor and are two processes that give access to the Tor network.
Stage 1: Malicious code execution
SimpleLocker waits for the BOOT_COMPLETED intent. When it occurs, it starts a service located in the MainService class. Starting the main activity with the launcher also starts the service. The service takes a WakeLock on the phone in order to get the device running the malware even if the screen goes off. Then, it schedules two repetitive task executors (MainService$3 and MainService$4) and launches a new thread (MainService$5). All these jobs are executed in the main process rg.simplelocker.
Stage 2: Communication with a remote server through Tor
A task executor MainService$3, that is launched every 180 seconds, sends an intent TOR_SERVICE to start the TorService class. If Tor is already up, the TorSender class is called to send the IMEI of the phone using the service. The TorService class is a huge class that setups linux executables that correspond to the libprivoxy.so and tor processes. The java code executes shell commands to copy and give executable permission to the files libprivoxy.so and libtor.so that come from the APK. The process is executed calling:
final String[] array = { String.valueOf(this.filePrivoxy.getAbsolutePath()) + " " + new File(this.appBinHome, "privoxy.config").getAbsolutePath() + " &" }; TorServiceUtils.doShellCommand(array, sb, false, false);
The libprivoxy.so process listens for HTTP requests on the port 9050. It is an HTTP proxy that filters and cleans the request generated and received by the tor client.
Stage 3: User’s data encryption
In the thread MainService$5, the malware encrypts all the multimedia files and deletes the original ones:
for (final String s : this.filesToEncrypt) { aesCrypt.encrypt(s, String.valueOf(s) + ".enc"); new File(s).delete(); }
The used algorithm is AES in CBC mode with PKCS#7 padding. The encryption key is constant, written in the code. Thus, we were able to generate a modified version of this malware where we have forced the decryption of the files.
The repetitive task MainService$4, checks in the SharedPreferences the value DISABLE_LOCKER that informs the malware that it should shut down in case the victim has paid. If not, it restarts the Main activity that displays in fullscreen a Russian message informing the user that its files have been encrypted and asking for a ransom.
Other resources
Triggering
Caracteristics
Malware type :
- Ransomware
Attacks :
-
 Confidentiality
Confidentiality
-
 Integrity
Integrity
-
 Availability
Availability
-
 Normal use
Normal use
Infection technique : Standalone application
Malicious code type :
- Use Java code
- Use native code
Hidding techniques :
- Not hidden
Triggering techniques :
- Executed at launch
- Waits for a particular intent
Samples
Java source code extracts:
MainService.java is the service started when the application is launched or the phone rebooted.MainService4.java is the repetitive task executed every 1 second in order to check if the ransom has been paid.
TorSender.java is the class used in the repetitive task MainService$3 in order to contact the C&C server.
HttpSender.java is the class that manages the requests and responses of the C&C server.
encrypt.java is the function used by the thread MainService$5 in order to encrypt user's files.
AesCrypt.java is the class that configures and executes the cipher algorithm.
Constants.java is the class that contains constant strings and values used by the malware.